HORMUZ WATCH
Tactical Maritime Domain Awareness Through
Edge-First Multi-Sensor Data Fusion
Edge-First Multi-Sensor Data Fusion
PHILLY 250 MARITIME DEFENSE HACKATHON | MARCH 27-29, 2026
CLICK NAMES TO VISIT PORTFOLIOS
// CONTEXT
The Problem
12K+
miles of US coastline to monitor
21M
barrels/day through Strait of Hormuz
95%
of global trade moves by sea
300+
maritime security incidents per year
- Existing maritime surveillance is cloud-dependent, high-latency, and expensive
- Adversaries exploit gaps: AIS spoofing, dark transits, fast-boat swarms, mine-laying
- No edge-first solution exists for denied or degraded environments
// APPROACH
The Solution
"Sensor to commander with low latency on $500 of hardware with zero cloud dependency"
DETECT
Edge ML anomaly scoring on Raspberry Pi 5
Less than 15ms per report
Less than 15ms per report
RELAY
AES-256-GCM encrypted ESP32 mesh network with constant-rate cover traffic
ANALYZE
Local LLM on Jetson + RAG vault with 151 intel documents
ACT
Low-latency dashboard threat cards, zero cloud
// PIPELINE
System Architecture
// ML CORE
Anomaly Detection Engine
18.8M
real USCG AIS records trained on (NOAA, June 2024)
100%
recall on 5 real US maritime incidents
18 FEATURES PER REPORT
- 5 vessel-type z-scores (SOG, speed delta, heading, COG, time gap)
- 4 static features (name, class, dimensions, speed-size ratio)
- 3 location features (distance to lane, port, bridge)
- 4 windowed features (heading std, speed trend, COG std, anomaly count)
- Sliding window: last 20 reports per MMSI
ML ENSEMBLE ARCHITECTURE
- 0.6 x Isolation Forest (100 trees, 200K subsample)
- 0.4 x PyTorch Autoencoder (18 > 12 > 6 > 12 > 18, ONNX export)
- 82 distinct vessel types with per-type baselines
- Total model footprint: ~5MB
// DATA
Training Data Sources
NOAA MarineCadastre
Real USCG AIS, June 2024, 30 days
18.8M reports
NOAA Historical
Incident validation days (Mar-Jun 2024)
5 incident days
OFAC SDN List
Sanctioned vessels and entities
treasury.gov
AISstream.io
Live global AIS via WebSocket
Real-time API
IMB Piracy Centre
Incident coordinates and timelines
Public map
Published OSINT
NTSB, IMO, news, Wikipedia for incident reconstruction
28 reference docs
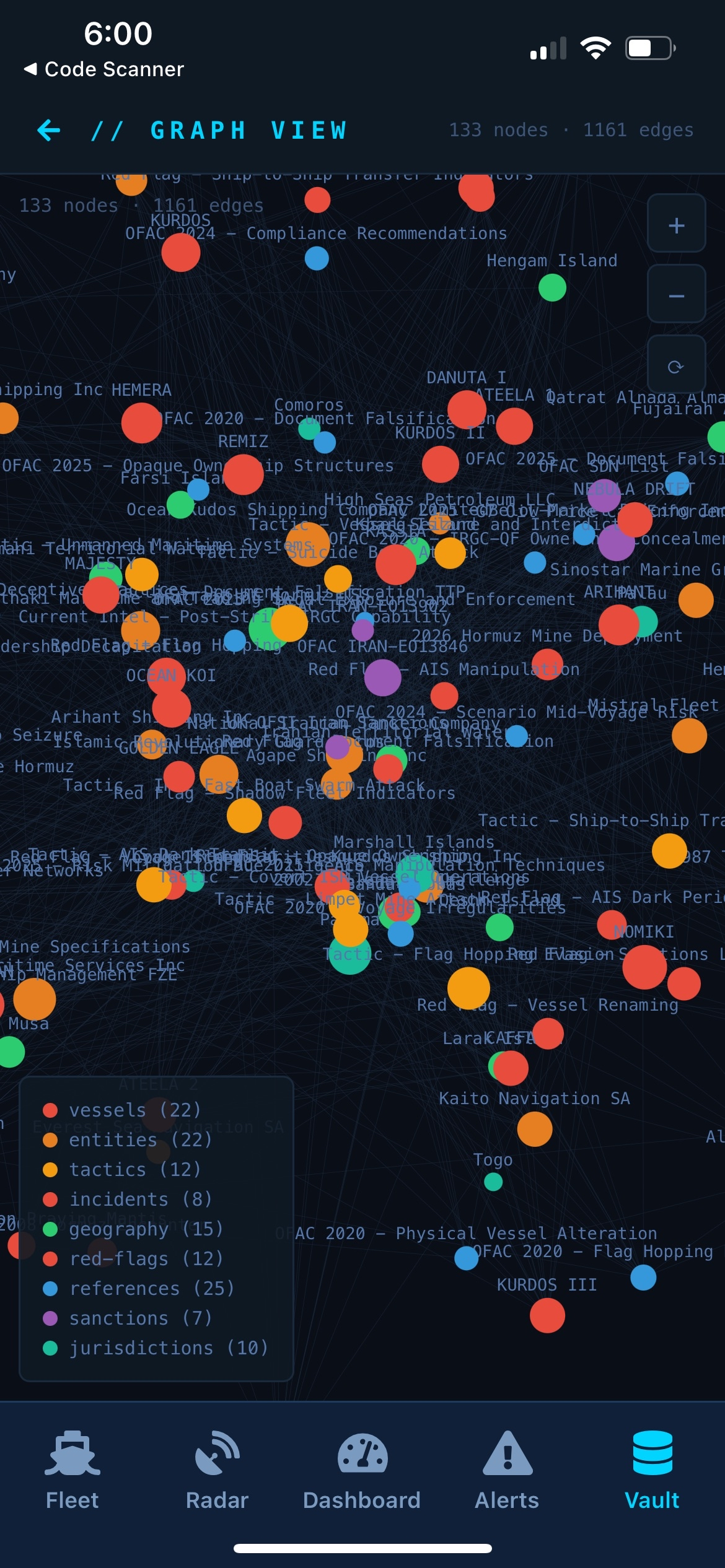
// INTELLIGENCE
The Vault: RAG Knowledge Graph
151 structured intel documents powering contextual threat assessment
11
Incidents
Stena Impero, Gulf of Oman, Fujairah, Mercer Street...
30
Vessels
Known good + known bad profiles with MMSI, flag, sanctions
26
Entities
IRGC, IRISL, 22 shell companies, ownership chains
16
Tactics / TTPs
Fast-boat swarm, AIS dark transit, limpet mine, drone strike
18
Geography
Hormuz, Bandar Abbas, Fujairah, shipping lanes with lat/lon
15
Red Flags
Behavioral and structural anomaly indicators
10
Sanctions
OFAC advisory context and SDN mappings
28
References
Intel reports, published analysis, OSINT
Alert triggers vault query → top-5 chunks retrieved → Phi3 Mini on Jetson generates threat assessment
Ties into scraper pipeline: OFAC SDN, open-source intel, and incident databases feed the vault
Ties into scraper pipeline: OFAC SDN, open-source intel, and incident databases feed the vault
// COMMAND NODE
Jetson Orin Nano: Command Node
HARDWARE
- Orin Nano, JetPack 6.x, ~$250
- Ollama + Phi3 Mini (4GB, runs locally)
- FastAPI + uvicorn on port 8000
- WebSocket push to all connected dashboards
- Rule-based fallback if LLM unavailable
RAG INTEGRATION
- Vault indexed at startup (151 markdown files)
- Keyword search ranks chunks by term frequency
- Top-5 chunks injected into LLM prompt (~2000 chars)
- Generates: threat level, indicators, historical precedent
- Output: structured FLASH threat card to dashboard
// COMMUNICATIONS
ESP32 Encrypted Mesh Network
238-BYTE PACKET STRUCTURE
AES-256-GCM
Every packet encrypted
238 bytes fixed size
Tamper = auth fail
238 bytes fixed size
Tamper = auth fail
ESP-NOW
2.4GHz peer-to-peer
~150m WiFi range
2-15km with LoRa
~150m WiFi range
2-15km with LoRa
COVER TRAFFIC
Dummy packets 5s interval
Defeats traffic analysis
Real/fake indistinguishable
Defeats traffic analysis
Real/fake indistinguishable
SERIAL FRAMING
[0x7E] [2B len] [data] [0x7E]
USB to wireless bridge
State-machine parser
USB to wireless bridge
State-machine parser
// SCENARIOS
5 Hormuz Incident Replays
Real incidents reconstructed as AIS replay scenarios for live demo
1
Stena Impero Seizure
Jul 2019
3 fast boats at 35kt, tanker AIS blackout, forced course reversal to Iran
2
Gulf of Oman Tanker Attacks
Jun 2019
Front Altair + Kokuka Courageous hit by limpet mines, rapid deceleration
3
Fujairah Port Sabotage
May 2019
4 tankers at anchor, 2 go dark simultaneously, coordinated AIS gaps
4
Mercer Street Drone Attack
Jul 2021
3 drone strikes over 2 days, 20-min AIS gap, vessel slows to 3kt
5
Mine-Laying Patrol
Iran Ajr
Unnamed Class B at 3kt, stop-start every 500m in shipping lane
All 5 incidents detected by the ML ensemble with correct severity classification. 672 total AIS reports.
// LIVE DEMO
System Demo
EDGE DETECTION
- AIS data flows into Pi edge nodes: Larak + Fujairah sectors
- Green = normal traffic, Red = anomalies
- Pi nodes glow on detection with MMSI and severity
ENCRYPTED MESH
- Alerts encrypt via AES-256-GCM, relay through ESP32 mesh
- Cover traffic makes real/dummy packets indistinguishable
LLM ANALYSIS
- Jetson pipeline: DECRYPT > ENRICH > CORRELATE > ASSESS
- RAG vault (151 docs) feeds Phi3 Mini threat assessment
- FLASH threat card pushed to dashboard via WebSocket
// DASHBOARD DEMO
Hormuz Watch Demo
LIVE DASHBOARD
- Leaflet map of Strait of Hormuz with TSS lanes
- Vessel tracking with color-coded threat classification
- Real-time alert feed with severity levels
INCIDENT REPLAY
- 5 real Hormuz incidents replayed through the scoring pipeline
- Anomalies detected and classified in real time
THREAT CARDS
- LLM-generated threat assessments with vault context
- Recommended actions pushed to operator screen
// MOBILE APP
React Native Mobile App
Built with Expo, 5 tabs for full tactical awareness on the go
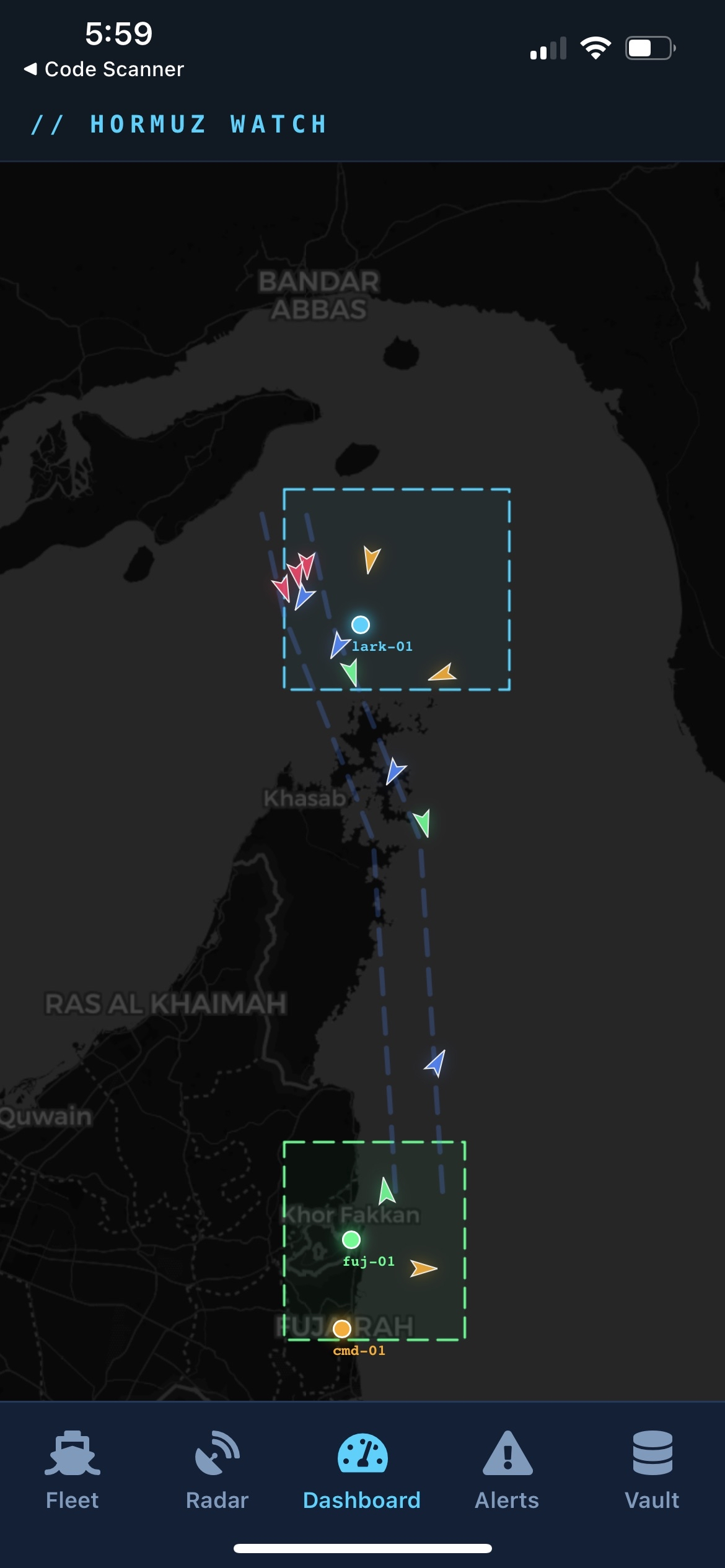
DASHBOARD
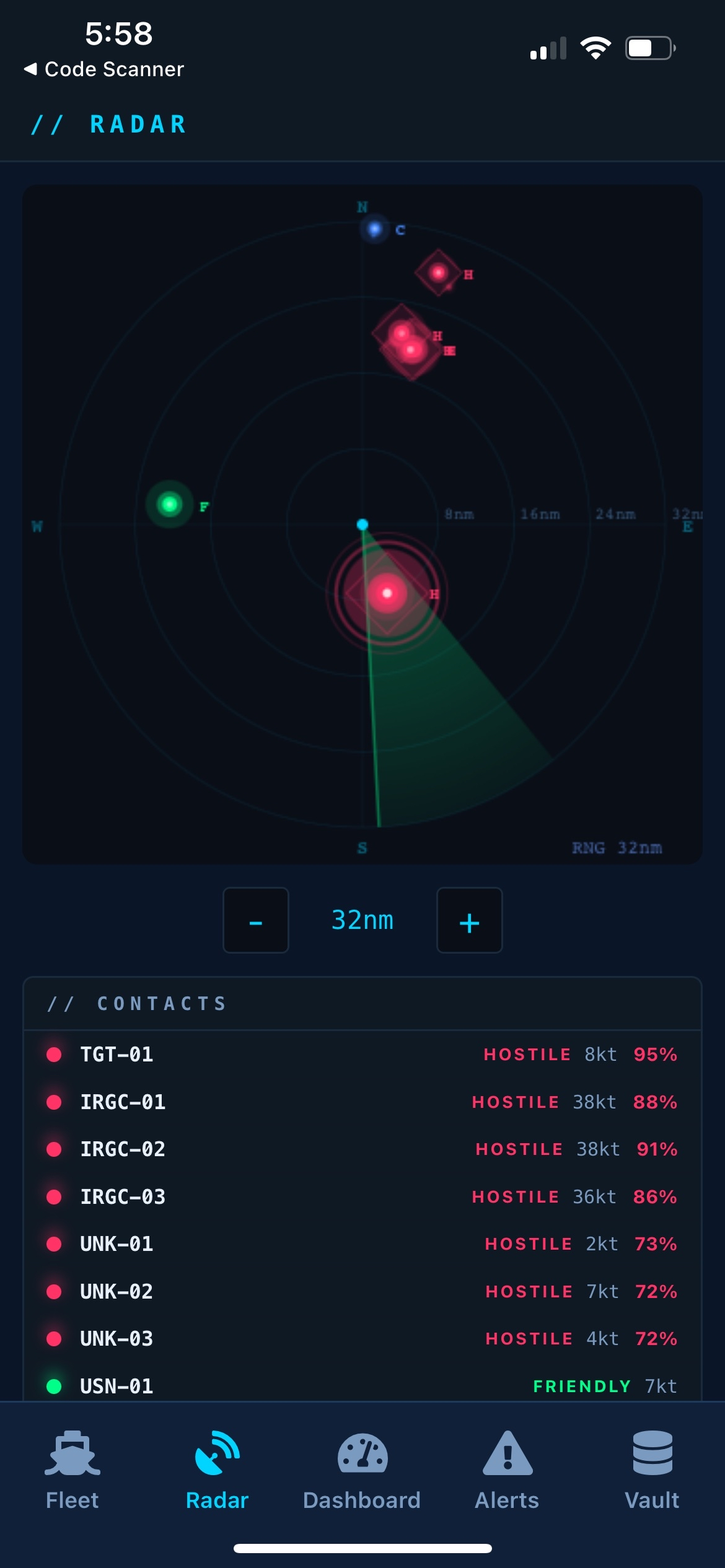
RADAR

FLEET
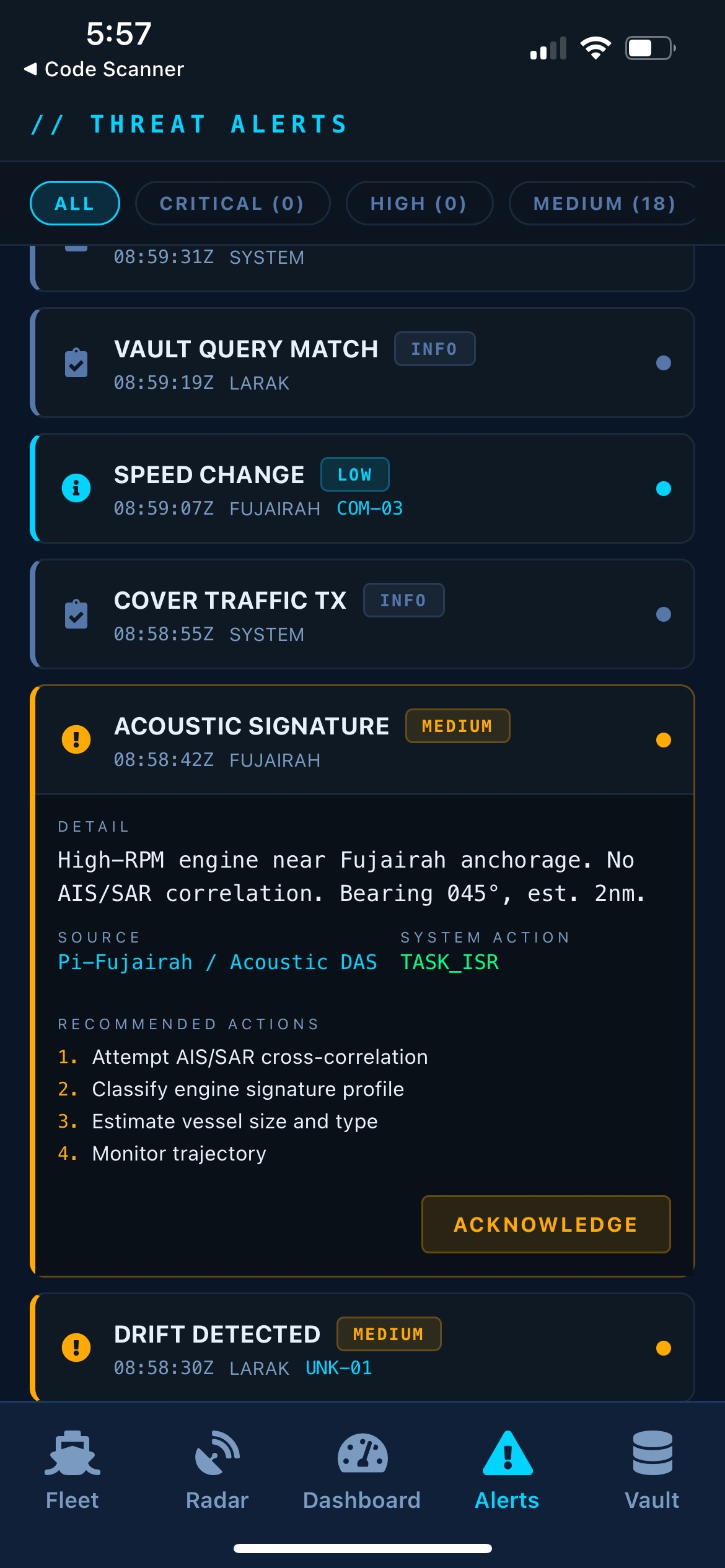
ALERTS
VAULT
// PROOF
Validation Results
All tests PASS, real data, real incidents
5/5
real incidents
detected
detected
100%
recall
(ML-only)
(ML-only)
137
reports/sec
throughput
throughput
8/8
validation
tests PASS
tests PASS
MV DALI (Baltimore Bridge)
Score -0.586
Top 6.1%
APL Qingdao (Chesapeake)
Score -0.408
Top 22.4%
Pelican Island (Galveston)
287/607 flagged
Bridge strike
MSC Michigan VII
Score -0.406
Top 12.6%
M/V Michipicoten (Lake Superior)
Score -0.554
Top 35.7%
// ECONOMICS
Cost + Scalability
HARDWARE COST
2x Raspberry Pi 5 (16GB)
$150
1x Jetson Orin Nano
$250
3x ESP32
$30
Antennas + cables
$20
TOTAL HARDWARE
~$450
WHY THIS MATTERS
- Cloud dependency: $0, runs fully offline
- Deployment footprint: less than 20MB total
- Nodes are disposable and independently replaceable
- Add a zone = add a $75 Pi + $10 ESP32
- Scales from single laptop demo to multi-zone mesh
- Graceful degradation at every layer
HORMUZ WATCH
Edge-first. Zero cloud. Low-latency detection.
$450 HARDWARE
<20MB DEPLOY
100% RECALL
PHILLY 250 MARITIME DEFENSE HACKATHON | MARCH 27-29, 2026
Thank You
CLICK NAMES TO VISIT PORTFOLIOS